A joint advisory has been released by cybersecurity agencies in Australia, Canada, Germany, Japan, New Zealand, South Korea and the U.S. regarding APT40 a cyber espionage group associated with China.
The warning is about their capability to seize opportunities including newly disclosed security flaws within hours or days of being made public releases for exploitation purposes.

According to the agencies, APT40 has targeted organizations in multiple countries such as Australia and the United States.
They also highlight that one of their remarkable strengths is their capability to promptly modify and apply vulnerability proofs-of-concept (PoCs) for conducting targeting, reconnaissance, and exploitation operations.
Bronze Mohawk
Since at least 2011, the adversarial collective also referred to as Bronze Mohawk, Gingham Typhoon (formerly Gadolinium), ISLANDDREAMS, Kryptonite Panda, Leviathan, Red Ladon,T A423 and TEMP.Periscope has been carrying out cyber attacks on entities in the Asia-Pacific region. It’s believed that this group is located in Haikou.
July 2021
Members of a hacking group were indicted by the U.S. and its allies for conducting a multiyear campaign targeting various sectors in order to steal trade secrets, intellectual property, and valuable information. The group was officially linked with China’s Ministry of State Security (MSS).
APT40 has been connected with waves of intrusion in recent years, which have carried out the ScanBox reconnaissance framework and utilized a security vulnerability in WinRAR (CVE-2023-38831, CVSS score: 7.8) as part of a phishing campaign aimed at Papua New Guinea. This operation resulted in BOXRAT backdoor installation on targeted systems.
March
The New Zealand government identified the culprit responsible for breaching both Parliamentary Counsel Office and Parliamentary Service during this year.
new exploits
According to the authoring agencies, APT40 detects fresh vulnerabilities in commonly used public software like Log4j, Atlassian Confluence and Microsoft Exchange with an objective of attacking their infrastructure.
The group APT40 frequently executes surveillance on networks that pique their interest, even those situated within authoring agencies’ nations. Their aim is to discover chances for attacking targets.
Conducted routinely, this reconnaissance readies the organization to spot exposed or outdated devices in these targeted networks and swiftly utilize exploits against them.
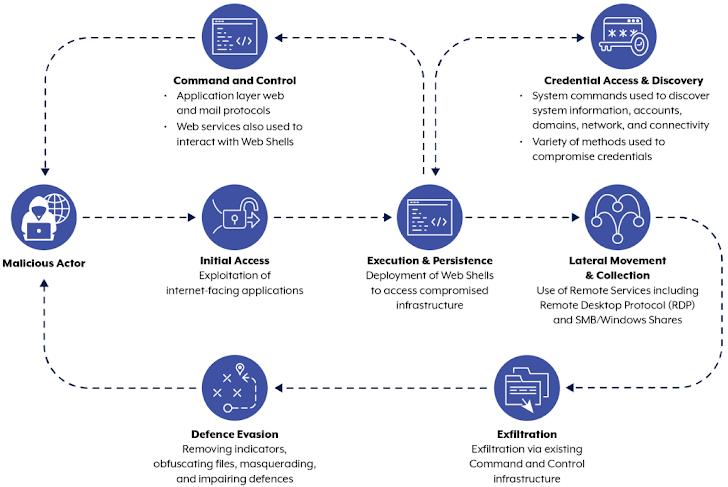
One of the noteworthy techniques utilized by the hacking team backed by a government is their utilization of web shells for establishing persistence and retaining entry to the target’s system, along with leveraging Australian sites as command-and-control (C2) centers.
Observations reveal
That it is deploying outdated or unpatched equipment, including small-office/home-office (SOHO) routers to manipulate its attack infrastructure and reroute malicious traffic in order to avoid detection. This mode of operation closely resembles the tactics used by other Chinese groups like Volt Typhoon.
Mandiant, which is owned by Google, reports that cyber espionage originating from China has undergone a significant evolution.
The objective now is to emphasize stealthiness in operations through the weaponization of network edge devices along with operational relay box (ORB) networks and living-off-the-land (LotL) techniques. This approach helps the attackers go undetected more easily.
conclusion
To expand on the attack chain, one would conduct reconnaissance, escalate privileges and move laterally by making use of remote desktop protocol (RDP) to pilfer essential credentials as well as extract desired data.
To minimize the dangers associated with these types of threats, it is advised that institutions uphold sufficient logging mechanisms, impose multi-factor authentication (MFA), establish a resilient patch management system, swap out equipment that has reached its end-of-life cycle, deactivate inactive services and ports as well as protocols while partitioning networks to restrict access to confidential information.







well documented content….
Good idea
I like reading it
I enjoyed reading this article.